Data Security with Snowflake: Row Access, Masking, and Projection Policies
Cloudyard
NOVEMBER 1, 2024
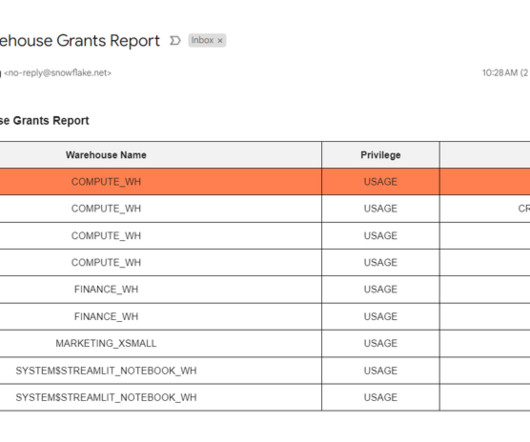
However, due to compliance regulations, access to these fields needs to be restricted based on the user’s role. However others can still use them for joins or aggregations but without viewing the data directly. Challenge: The Audit Team requires full access to sensitive columns like Customer Number for compliance checks.












































Let's personalize your content