The Pros and Cons of Leading Data Management and Storage Solutions
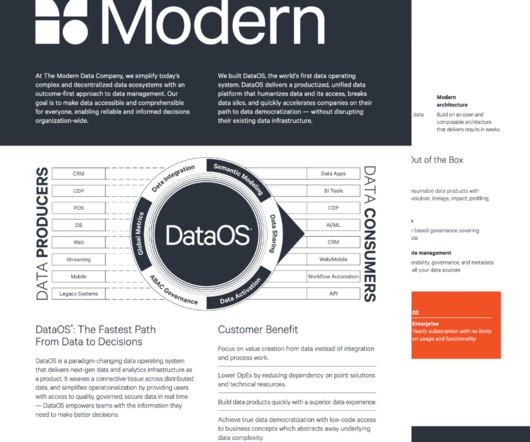
The Modern Data Company
MAY 8, 2023
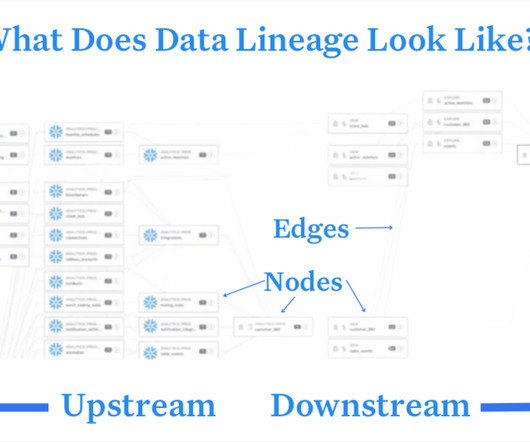
And by leveraging distributed storage and open-source technologies, they offer a cost-effective solution for handling large data volumes. In other words, the data is stored in its raw, unprocessed form, and the structure is imposed when a user or an application queries the data for analysis or processing.










Let's personalize your content